From the creators of BloodHound FOSS and Powered by SpecterOps research, a focused approach to Attack Path Management
Why Us
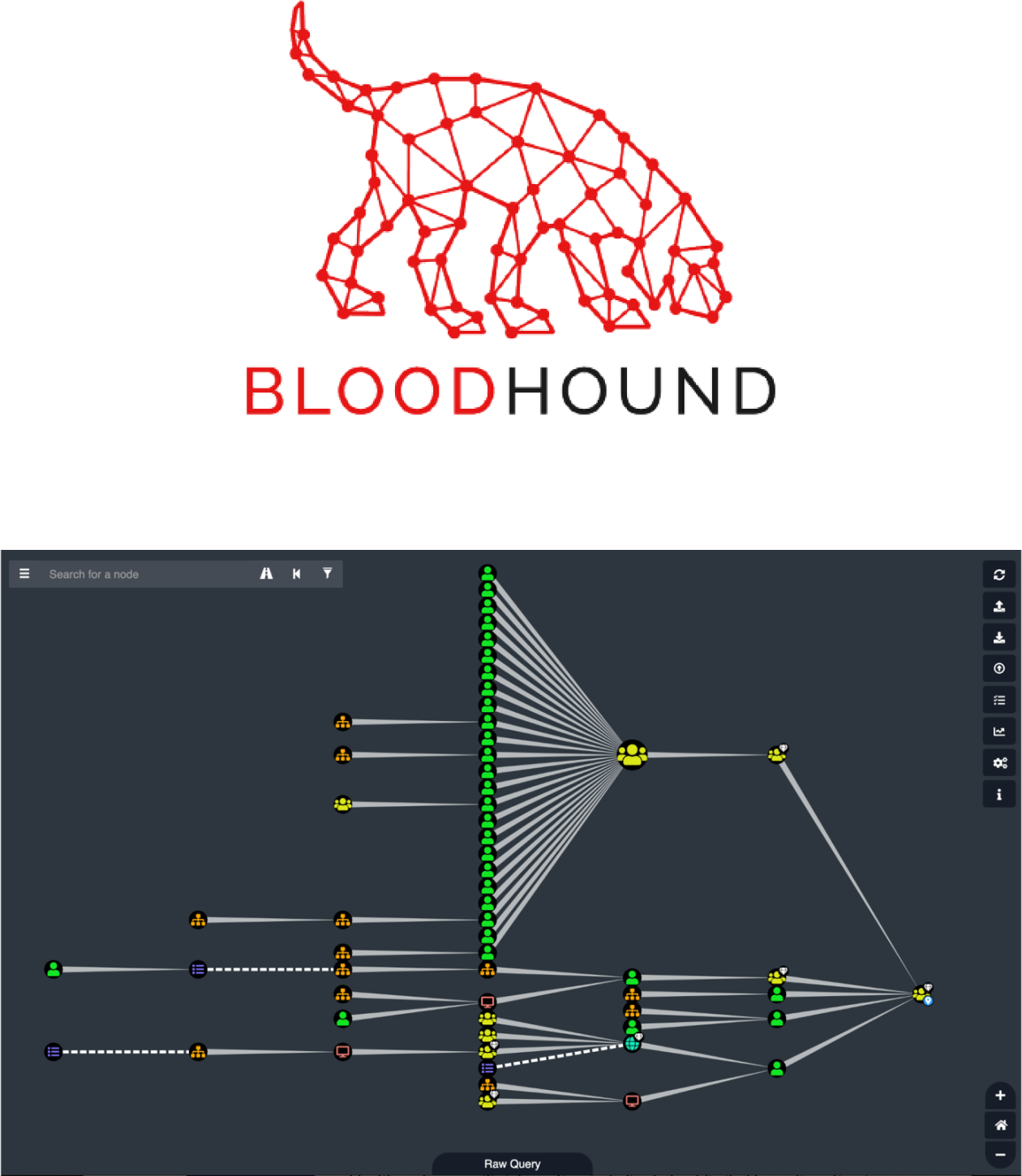
BLOODHOUND
Where it all started
Andy Robbins, Rohan Vazarkar, and Will Schroeder first created BloodHound FOSS in 2016 to empower penetration testers and red teamers to illustrate adversary risk to organizations and help defenders be prepared for imminent attacks. Since then, BloodHound has been used by attackers and defenders alike to identify and analyze Attack Paths in both on-prem Active Directory and Azure AD environments.
Attackers can use BloodHound to easily identify highly complex Attack Paths that would otherwise be impossible to quickly identify. Defenders can use BloodHound to identify and eliminate those same Attack Paths. Both blue and red teams can use BloodHound to easily gain a deeper understanding of privilege relationships in an AD or Azure environment.
Community Driven: BloodHound Enterprise also facilitates continued open-source technical capability and research within Active Directory and Azure AD.
Why BloodHound Enterprise
Almost immediately after BloodHound FOSS was released, the creators and many others realized that the potential for the tool was far more compelling on the defensive side than it was on the offensive. However, as BloodHound FOSS was designed and architected for a different use case, the team knew a different solution was required.
Where BloodHound FOSS is designed to identify Attack Paths to exploit, the team had the vision to design BloodHound Enterprise to manage all Attack Path risks continuously and comprehensively such that:
- Attackers are forced to go elsewhere and use different tactics that are more difficult and have less payoff than they do today.
- Least privilege access, tiered administration and credential hygiene are attainable, effective best practices.
- Enterprises can measure, assess, and improve their security posture.
What Enterprise Will Achieve
BloodHound Enterprise benefits
With the introduction of BloodHound Enterprise, the team redefines Active Directory and Azure AD security by enabling Attack Path Management.
Unprecedented visibility into Active Directory and Azure AD
Visualize privileges for instant clarity on AD and Azure AD architecture.
Best practices made practical
Tiered administration, least privilege, and credential hygiene are now possible.
Active Directory and Azure AD security for everyone
Efficiently harden Active Directory and Azure AD against abuse.
Elimination of ‘band-aid’ fixes
Directly address the risk of Attack Paths at precise Choke Points rather than fighting misconfiguration debt.
Measurably improve security posture
Meaningful, transparent measurements that illustrate the risk reduction gained from Attack Path Management.
