From the creators of BloodHound, an Attack Path Management solution that continuously maps and quantifies identity Attack Paths in Active Directory and Azure with visualization and detailed attack path analysis. Remove millions of Attack Paths within your existing architecture and eliminate the attacker’s easiest, most reliable, and most attractive target.
Attack Paths are a
problem.
[big]
[difficult]
[complex]
[serious]
EASY. RELIABLE. EFFECTIVE.
Attack Path Management for all types of attacks
Why are Attack Paths a problem?
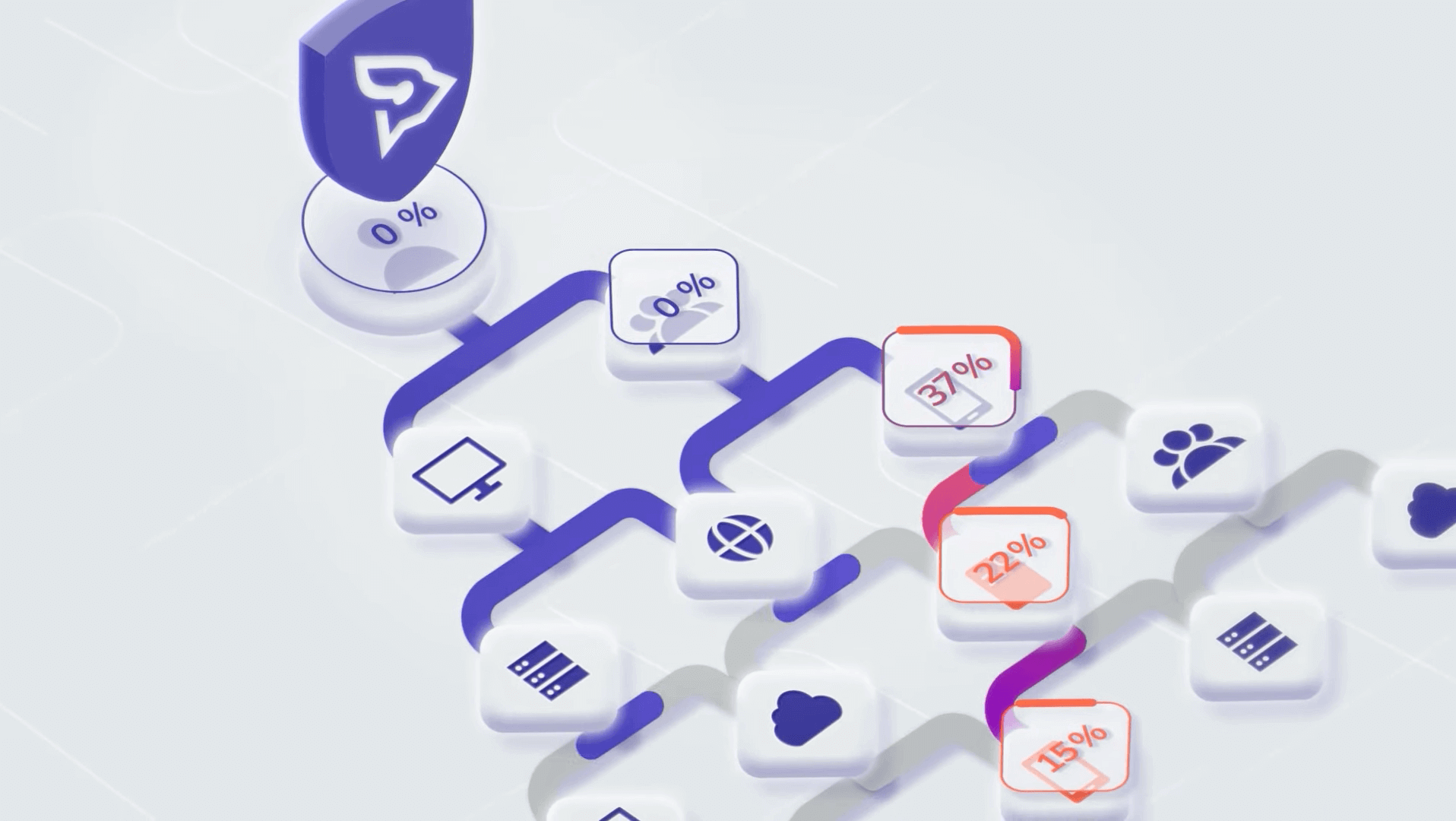
ATTACK PATH VISUALIZATION
How BloodHound Enterprise works
- Continuous Attack Path mapping
- Prioritize and quantify Attack Path Choke Points
- Precise, practical remediation guidance
- Monitor Attack Paths and measure improved security posture
QUIT FOCUSING ON GENERIC TYPES OF ATTACKS
Start addressing impact of Attack Paths
Unprecedented visibility into Azure AD
Visualization of privileges for instant clarity within Azure AD
Best practices made practical
Tiered Administration, Least Privilege, and Credential Hygiene are now possible
AD and Azure AD Security for everyone
Harden AD and Azure AD against abuse and improve directory services availability