Introducing BloodHound 4.1 — The Three Headed Hound
Introducing BloodHound 4.1 — The Three Headed Hound
Prior Work
Analyzing Active Directory attack paths using graph theory is not a new concept. Prior work includes the following:
Heat-ray by John Dunagan, Alice Zheng, and Daniel R. Simon (2009)
Airbus BTA by Philippe Biondi, Joffrey Czarny, Xavier Mehrenberger, and Nicolas Bareil (2013)
Active Directory Control Paths by Emmanuel Gras and Lucas Bouillot (2014)
Acknowledgments
This release includes direct and indirect contributions from the following people:
Lucas Pereira (@vulcanunsec)
Luke Roberts (@rookuu_)
Elad Shamir (@elad_shamir)
Ari Ugwu (@ari_ugwu)
Marcello Salvati (@byt3bl33d3r)
Three New Edges in 4.1
With BloodHound 4.1, we’re introducing three new edges into the attack graph:
AddKeyCredentialLink provides a greatly simplified object takeover primitive against User and Computer type nodes, based on research and work by Elad Shamir and Michael Grafnetter.
Attackers can easily abuse this relationship using Whisker and Rubeus, as seen in this example video:
Defenders can prevent this abuse by removing write access to the msDS-KeyCredentialLink on the affected object, along with any other abusable permission that can result in write access to that property. Defenders can alert on this attack taking place by analyzing Windows events 4768 and 5136. More details are available in this post by Elad Shamir.
AddSelf covers a blind spot we had in BloodHound, where we were not collecting the permission where a user or group can add themselves, and only themselves, to a particular security group. Thank you to Luke Roberts for pointing this out and submitting a PR.
WriteSPN covers the particular write privilege to the ServicePrincipalNames attribute, letting you know when you already have the targeted kerberoasting opportunity against a user.
These three new edges may not seem like a lot, but the impact to attack paths tracked by BloodHound can be astronomical — literally. In this Twitter thread, I explain how the impact of adding new node or edge types can increase the number of attack paths in a database to easily exceed the estimated number of particles in the known universe:
— @_wald0
Quality of Life Improvements
Along with the above new edges, we have some important quality of life improvements as well:
- Data ingestion via the BloodHound GUI is now much faster
- Data collection with SharpHound is more accurate, consistent, and faster
- The -SearchForest flag is back, letting you easily enumerate all domains you can reach
Introducing SharpHound Common
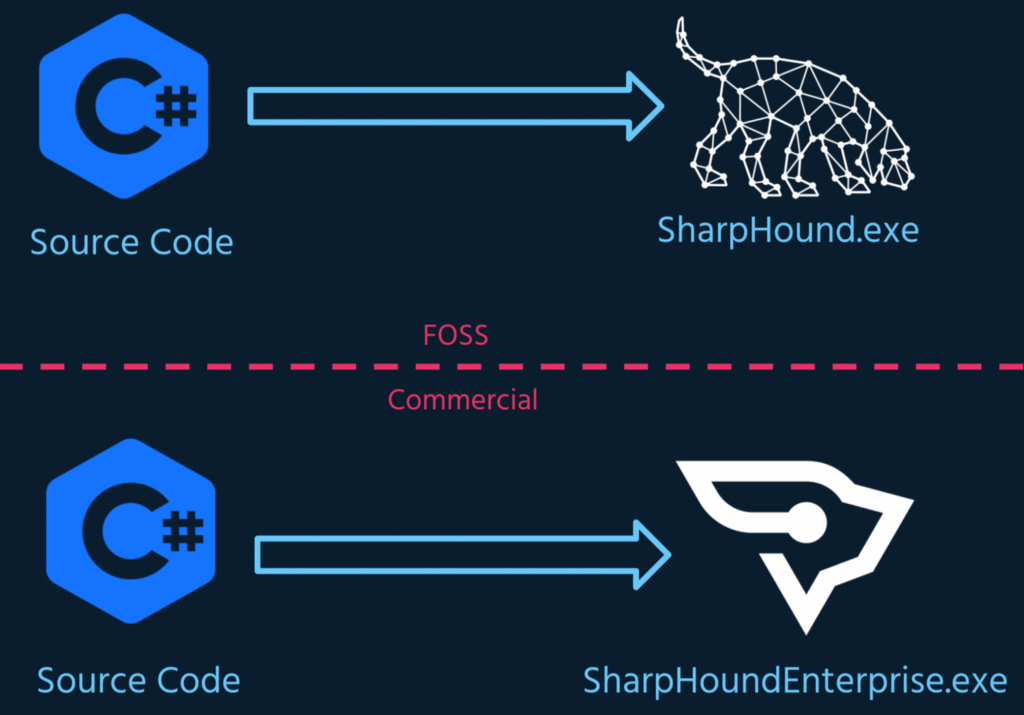
Arguably the biggest part of this update is the introduction of SharpHound Common. Historically, FOSS SharpHound and SharpHound Enterprise were built from two wholly distinct code bases:
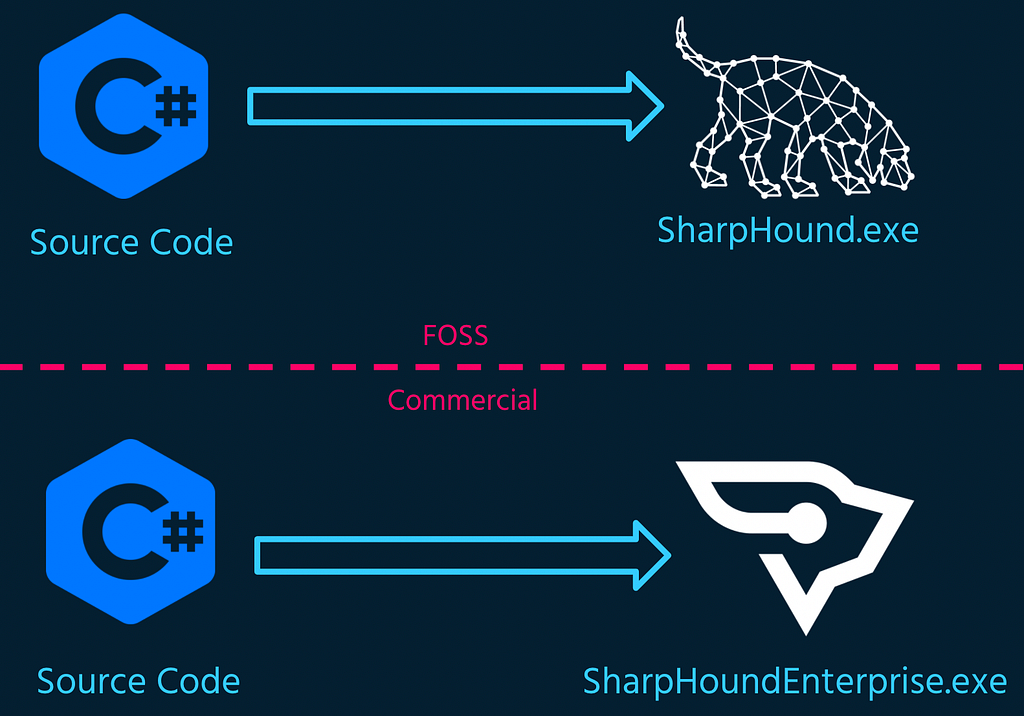
Today we’re introducing SharpHound Common: one code base from which both FOSS SharpHound and SharpHound Enterprise are built:
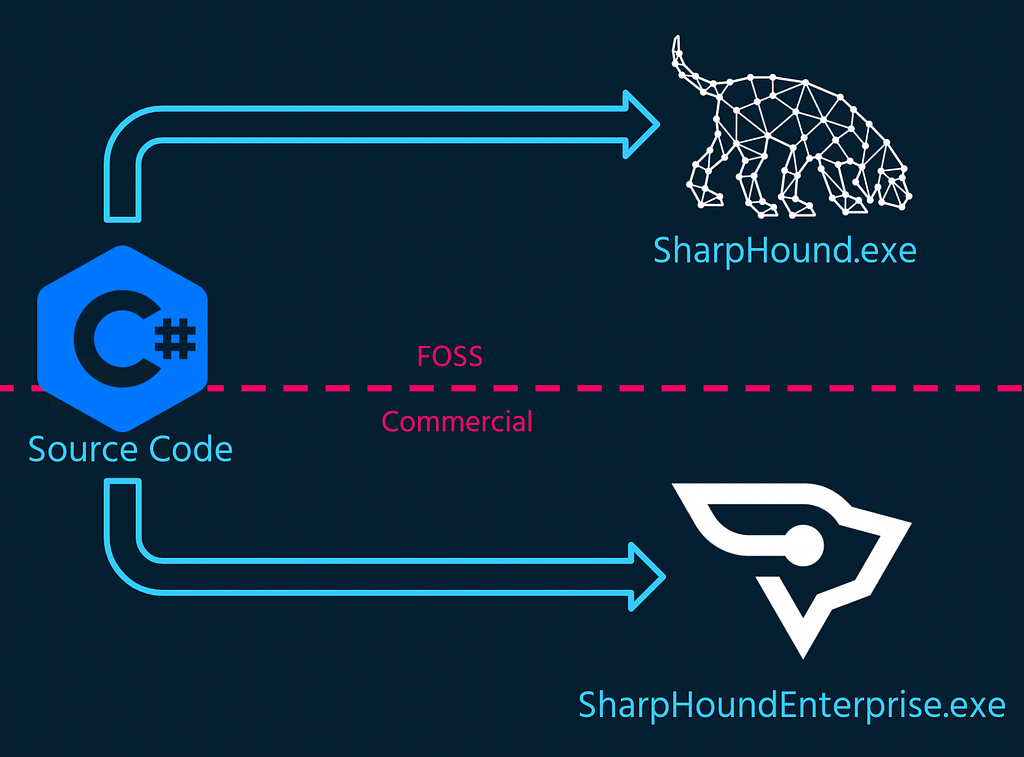
The marriage of these code bases enables several exciting things:
- Vastly improved documentation to help OSS developers work with and build on top of SharpHound (SharpHound Common is GPLv3 licensed).
- Automatic testing and reporting which measurably improves the quality and stability of SharpHound for everyone.
- Delivering high quality data collection capabilities to Enterprise customers instantly benefits the FOSS community.
You can start seeing those benefits today, as FOSS SharpHound is now faster, more accurate, and more stable thanks to the new SharpHound, a ground-up rewrite of BloodHound’s official data collector.
Announcing BloodHound Common
When we released BloodHound Enterprise in July of 2021, we made a firm, simple commitment that FOSS BloodHound would remain free and open source forever, and that we would continue development on FOSS BloodHound:
— @_wald0
Today we’re making good on that promise with the introduction of SharpHound Common, but there’s a lot more work ahead of us here. Today we’re announcing our intent to merge the other major pieces of the application, including the front-end GUI, middleware, and database:
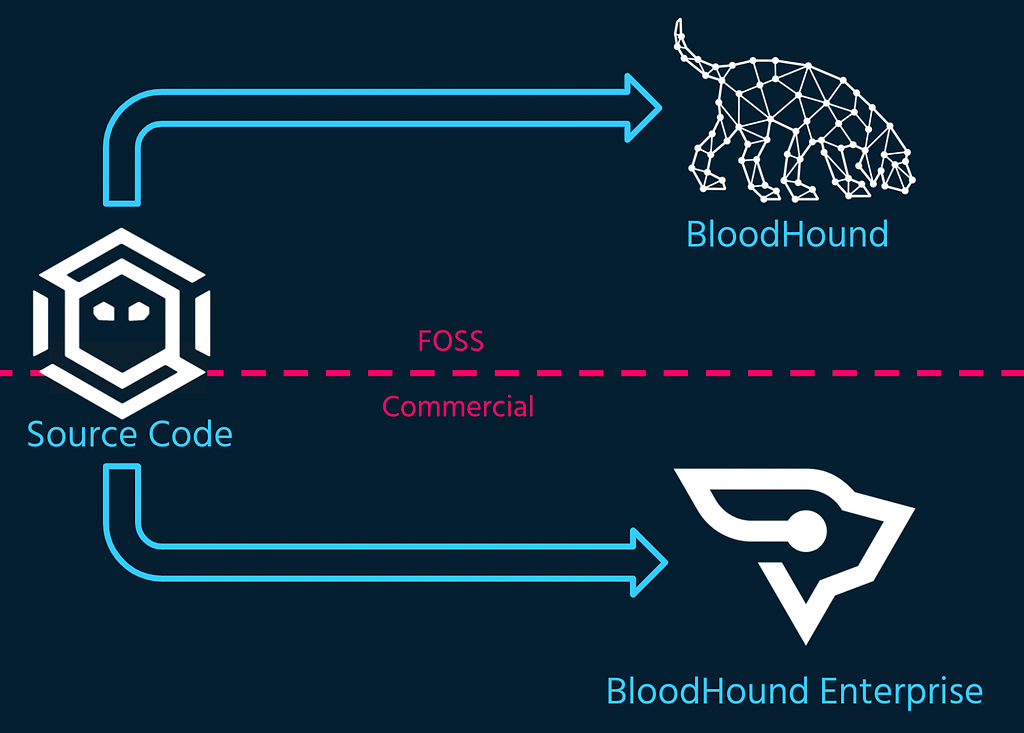
Our vision is to rapidly speed development, feature delivery, and bug fixes by funding FOSS BloodHound development with BloodHound Enterprise. This will dramatically increase stability, performance, and speed for both FOSS and Enterprise users.
FOSS BloodHound will remain focused on the red-team use-case, while BloodHound Enterprise will focus on helping our customers manage attack paths. The features that enable attack path management in BloodHound Enterprise will remain closed-source.
Future Work
So, what’s next? Immediately on the horizon we’re hoping to deliver the following in BloodHound Enterprise and FOSS BloodHound as soon as possible:
- Active Directory Certificate Services (AD CS) abuse primitives
- Azure API abuse primitives
- Way, way more Azure abuse primitives
Stay in touch with us by joining the BloodHoundGang Slack.
Download FOSS BloodHound today. Get started by reading the docs.
Read more about BloodHound Enterprise, or request a demo today.
Thank you Will Schroeder, Andrew Chiles for reviewing this post.
Introducing BloodHound 4.1 — The Three Headed Hound was originally published in Posts By SpecterOps Team Members on Medium, where people are continuing the conversation by highlighting and responding to this story.