Announcing Azure in BloodHound Enterprise
In July of 2021, we launched BloodHound Enterprise. Since then, our customers have been using BHE to easily identify and eliminate millions, even billions of attack paths in their on-prem Active Directory environments.
Today I’m happy to announce support for Azure in BloodHound Enterprise.
BloodHound Enterprise is an Attack Path Management solution that lets you quickly identify, eliminate, and manage attack paths in your on-prem Active Directory, your Azure tenants and subscriptions, and attack paths that bridge those platforms.
Why Attackers Target Azure
More and more organizations are migrating some or all of their identity, access, and endpoint management services into Azure, standing up identities, infrastructure and applications to support their business. Attackers have also noticed this trend see Azure today the way they’ve seen Active Directory for the last 20 years:
Azure is a foundational service that the entire business relies on. If the attacker takes full control of an Azure tenant, they gain full control of the business.
Azure is a ubiquitous product used by more than 95% of Fortune 500 businesses and beyond. Attackers learn how to attack Azure once, then use that knowledge against almost any organization on the planet.
Azure is a powerful collection of identity and infrastructure management tools at the attacker’s disposal to enable lateral movement, persistence, and data exfiltration.
Attack Paths in Azure
Azure services share similar names and concepts with their on-premises counterparts (for example, Azure Active Directory versus Active Directory), but these systems fundamentally differ in how they control access to securable objects, and even what those securable objects are in the first place.
While the systems themselves work differently, attack paths emerge all the same. I’ve written about how attack paths emerge around Service Principals, Azure APIs, and even how they can be used to pivot from Azure back down to on-prem Active Directory.
How BloodHound Enterprise Helps
BloodHound Enterprise is based on the three fundamental pillars of Attack Path Management:
- Continuous and Comprehensive Mapping of All Attack Paths
- Empirical Impact Assessment of Attack Path Choke Points
- Practical, Precise, and Safe Remediation Guidance
As an Attack Path Management solution, BHE offers several benefits:
- Elimination of Ineffective “Band-Aid” Fixes
- Measurable Security Posture Improvement
- Clear Visibility of Privileges in Azure
- Impractical Best Practice Made Practical
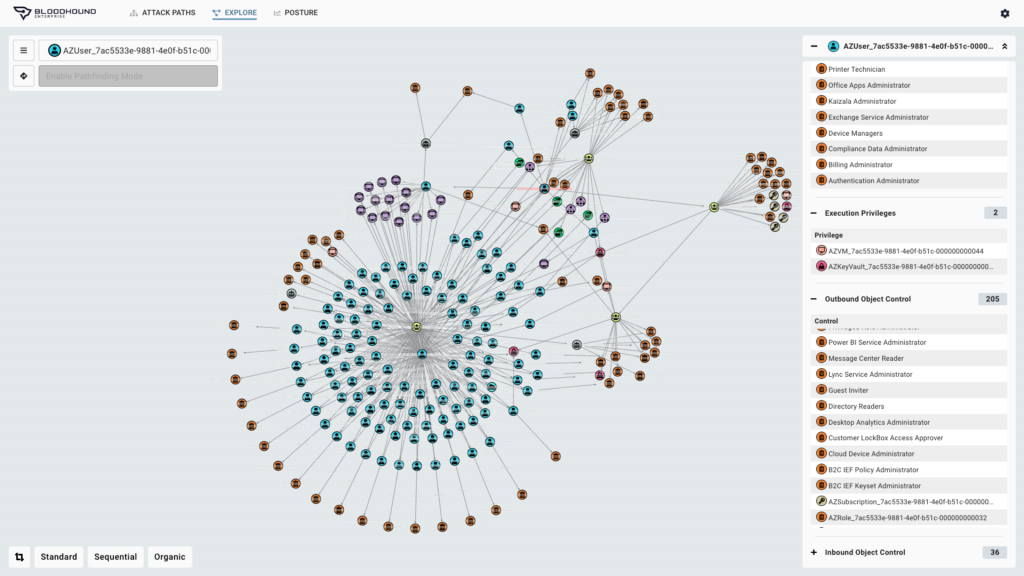
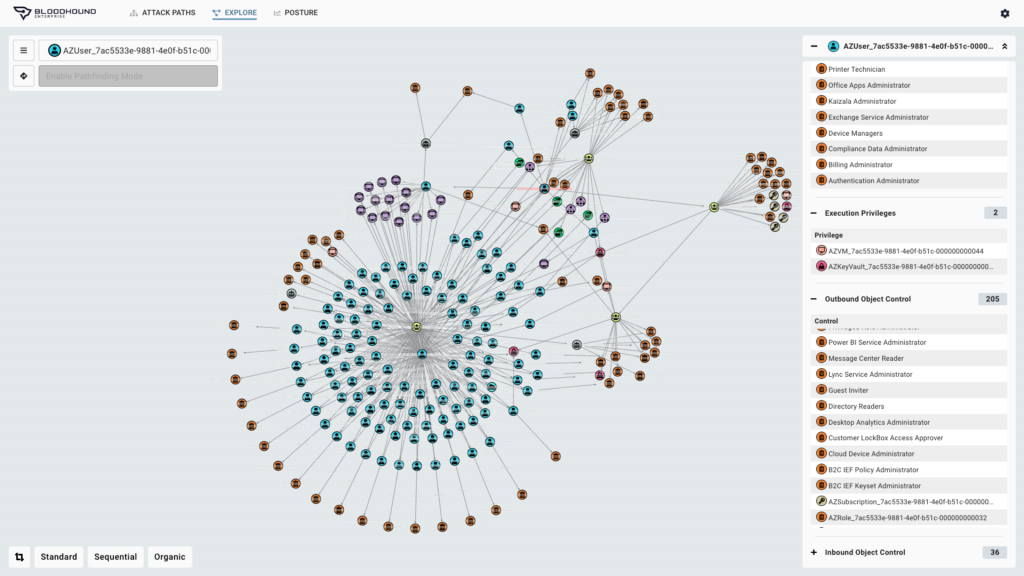
Additionally, BHE makes it easy to audit effective permissions against any object and find potentially dangerous connections to other identity platforms including other Azure tenants and on-prem Active Directory domains.
What’s next?
New attack path research is coming out all the time. As researchers identify new abuse primitives, we’ll be adding those into BloodHound Enterprise as well. I’ll share my own methodology for discovering new abuses in my talk at Insomni’Hack in Geneva next month.
Next month we will do a webinar showing off the new Azure features in BHE. You can register for that webinar here.
All current BloodHound Enterprise customers get early access to Azure support today, with general availability coming next month (April 2022). Not a BHE customer yet? Request a demo today.
Announcing Azure in BloodHound Enterprise was originally published in Posts By SpecterOps Team Members on Medium, where people are continuing the conversation by highlighting and responding to this story.